
Think Tank
Dealing With Intel’s Massive Security Flaw
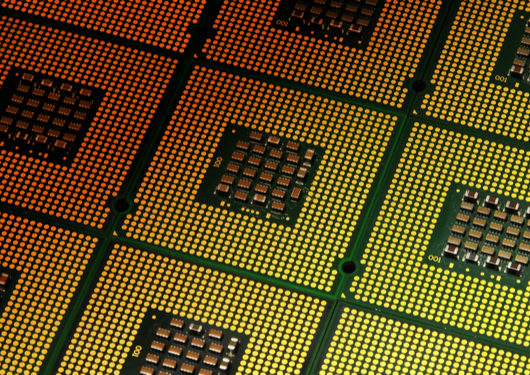
The announcement early this year of the security gap discovered in just about every computer made in the last 23 years had chipmakers and users alike scrambling for a patch. Major software vendors, including Microsoft and Apple, offered some quick fixes, but long-term protection could be years away, involving a wholesale redesign of the affected chips.
In the meantime, the vulnerabilities are said to expose modern processors to several potentially disastrous viruses, including Meltdown and Spectre. So what can be done in the short term, as we await a permanent solution?
So far, there do not appear to have been any attempts by hackers to exploit the flaw, says Tim Crosby, senior security consultant with Spohn Security Solutions. Users are more likely to find themselves dealing with performance and reliability issues, as chip manufacturers and software providers rush to plug the gap.
Interim patches are likely to slow down processors, Crosby says. The architecture that underlies all computing system puts a premium on computational speed — the very quality that appears to be making devices vulnerable to attack. Chipmakers are likely to install a compensating controller that will affect processor performance for a time.
The obsession with speed might well have blinded developers to the underlying flaws in the chips in question. A similar crisis emerged last year, when Wi-Fi networks using the WPA2 security protocol were found to be vulnerable to key reinstallation attacks, or KRACKS.
“We’re human,” says Crosby. “We build things, and we don’t anticipate every possible thing that could happen. [Intel and others] were focused on chip speed, not vulnerabilities.”
In the near term, Crosby recommends that users apply the offered patches “within reason.” Businesses should begin planning for the consequences of reduced chip speed — between 5 and 30 percent slower, if estimates by experts are to be believed. “You’re probably going to have to put additional resources in place to get the same computing power out of the system,” he says.
Clearly the disclosure of the chip flaw should serve as a wakeup call for designers and computer users alike. But the same could have been said for any of the major viruses or vulnerabilities to have emerged in recent years, including KRACK and last year’s WannaCry ransomware attack. The problem, it often seems, is public indifference or inaction in the face of these serious security threats.
With the emergence of cloud computing, the potential for serious damage has become greater than ever. Proponents of cloud technology have argued that it’s essentially secure. Nevertheless, says Crosby, “a lot of folks who wanted to migrate to the cloud to transfer risk are now finding out that server farms are the biggest probable target. It’s literally affecting everything and everybody.”
One layer of security isn’t enough, Crosby says. “You need levels across the board. And you need to pick up the slack when you identify where your vulnerabilities are.”
Users who find their systems threatened crave a “silver bullet” that will fix the problem quickly and painlessly. Such a solution doesn’t exist. Often, says Crosby, companies are better off allocating money for internal training, and leveraging the resources that they already have.
Yet many businesses don’t even have a policy for classifying which data is most critical, and should therefore be subject to the highest level of protection. A truly effective information security assessment, Crosby says, involves a deep dive into one’s level of compliance with rules such as HIPAA, or the Health Insurance Portability and Accountability Act, which sets standards for the protection of patient data.
Even more basic — and, sadly, often overlooked by users — is the need for strong passwords. Spohn often uncovers easily guessable passwords in its evaluation of clients’ security controls at multiple levels of their I.T. systems.
Business have their priorities backwards, Crosby says. “Most people start with compliance and assume you’re going to get security. Whereas if you shore up security, it leads to compliance.”
There’s no lack of outside experts to help guide companies through an I.T. security crisis. But a degree of internal expertise and control is also vital, says Crosby.
“Some organizations are not going to be large enough to have this,” he says. “But ideally, there should be a separate department that focuses on security and doesn’t fall under I.T. It should have a completely different reporting chain.” Such a setup eliminates the pushback that comes from I.T. staff complaining about the difficulties of implementing longer and more complex passwords.
“The decision to implement security controls can’t be unduly influenced by the operational impact it has,” Crosby says.
The ultimate responsibility for security must rest at the executive level, whether that’s a chief security, financial or technology officer. A truly effective program, Crosby stresses, “can’t be fostered unless it’s pushed from the top down.”






