
Cyberattacks can happen at any time, on any scale, and through any device that’s connected to the network. The longer a cyber breach goes on, the more it results in lost data, time and money.
A single cyberattack is enough to devastate a supply chain. Moreover, the effectiveness of credentials at each stage of the supply chain has a direct impact on every other part of the business.
According to the Cyber Security Breaches Survey: 2020, 46% of businesses have identified breaches or attacks within the last year. The survey notes that the most common type of cyberattacks are phishing attacks — e-mails received by staff that direct them to fraudulent websites.
“This is followed, to a much lesser extent, by impersonation and then viruses or other malware,” the survey says. “One of the consistent lessons across this series of surveys has been the importance of staff vigilance, given that the vast majority of breaches and attacks being identified are ones that will come via [those types of attacks].”
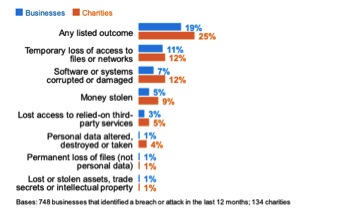
For small businesses that are part of a supply chain, the report makes clear the importance of possessing knowledge of cybersecurity by everyone with access to the network, each of whom can be considered a viable target for attackers. The impact of these attacks can be seen in the image below, taken from the report.
Phishing involves a socially engineered attack where a threat actor masquerades as a trusted entity. The recipient of an e-mail, phone or text message is misled into providing sensitive information by who they believe is a trusted person.
This method of attack is usually accomplished by luring the victim into clicking a malicious link, which in turn enables the installation of malware, ransomware, or the revealing of sensitive personal data such as passwords and credit card details.
Some of the most sophisticated recent phishing campaigns have come from individuals acting as representatives of the U.S. Centers for Disease Control and Prevention (CDC) and World Health Organization (WHO).
The cyber breaches survey shows a 70% increase in attacks detected by people — not technology. The latter can detect when something is obviously wrong, but it’s looking for facts rather than intent. Studies show technology stops about 999 out of 1,000 phishing and virus-containing e-mails. But the ones that get through are often those that don’t look wrong from a technology perspective. The invitation to log onto a fraudulent website appears legitimate. It’s only when the context of the message and website are read by a human that it can be identified as a threat.
Technology support is coming, in the form of artificial intelligence and active defense campaigns by governments. For now, however, it falls on us as users to identify the threat. That’s why education for all staff is essential.
Each partner in the supply chain is dependent on all others, and that’s especially the case with cybersecurity. You don’t want to be the one who gets the first virus, which then infects the rest of your chain and partners, and eventually impacts customers.
All businesses must take care to practice good cybersecurity processes to prevent this type of spread. Only then can they ensure security from top to bottom, and guard against the possibility of an attack like the 2017 M.E.Doc Software Hack.
All employees should be aware of the telltale signs of phishing, whom to report potential security issues to, and any request that seems unusual or out of the ordinary, especially if there’s a perceived urgency accompanying it. Here are five steps employees should take to guard against potential attacks:
- Create long and unique passwords (more than 12 characters).
- Use two-factor authentication wherever possible.
- Educate yourself on the telltale signs of phishing.
- Never share sensitive information with someone who calls you unexpectedly. Check who they are, find a contact number from some other source (e.g., and invoice or website), and call them back.
- Double-check anything that seems unusual, especially when being asked to do something outside normal processes.
With every employee in the business adhering to cybersecurity processes and remaining vigilant at all times, especially about the use of personal equipment that’s connected to the network, there’s a 70% less chance of experiencing a successful attack.
Education is key to keeping your business safe. Technology can only do so much to help. Ultimately it will always come down to staff taking ownership of security and potential threats, and knowing how to combat them in the correct manner. That ability only comes from education and investment in coordinated, strategic processes for ensuring strong cybersecurity.
Colin Robbins is managing security consultant at Nexor.







